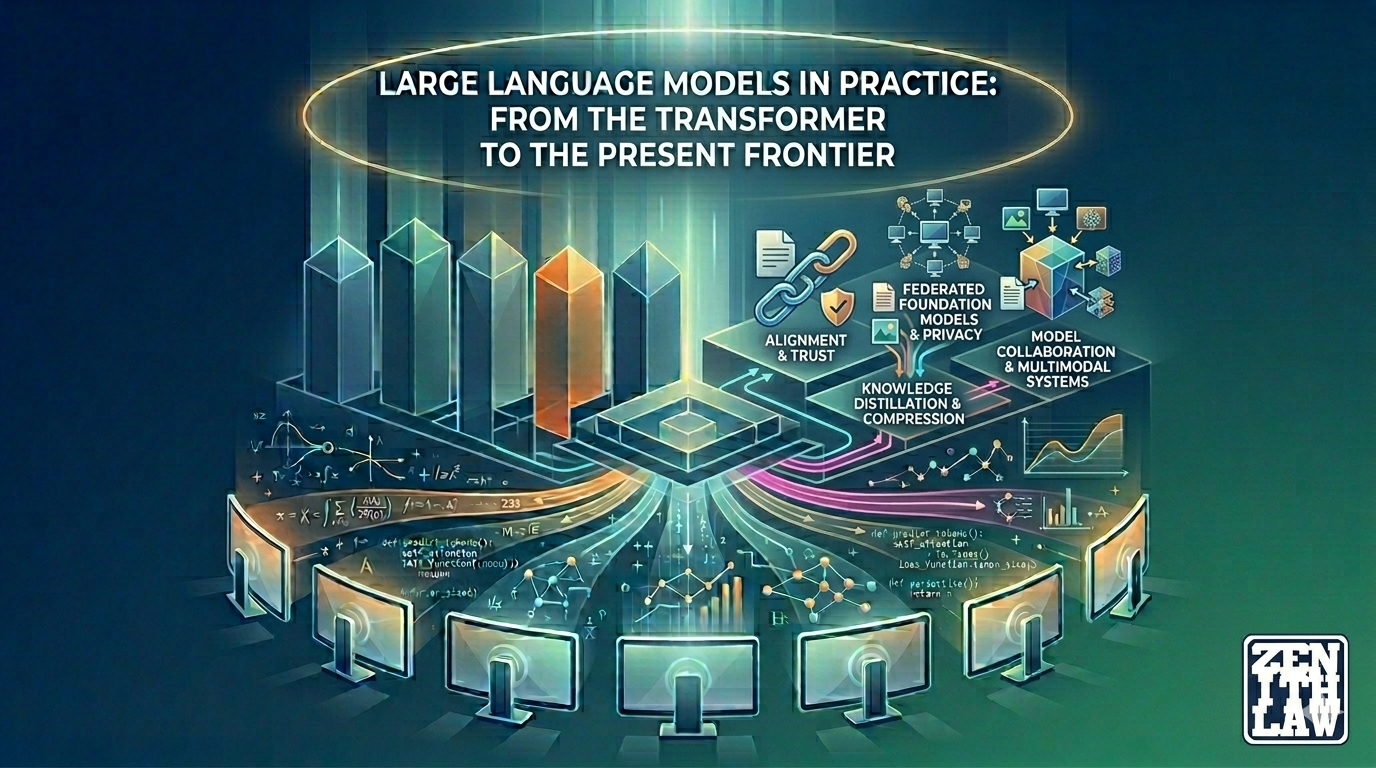
Published 12 April 2026 by Zenith Law
This article synthesizes insights from nine educational videos and nine scholarly works on large language models. It traces the evolution from the 2017 Transformer paper through GPT-3, alignment research, knowledge distillation, federated learning...
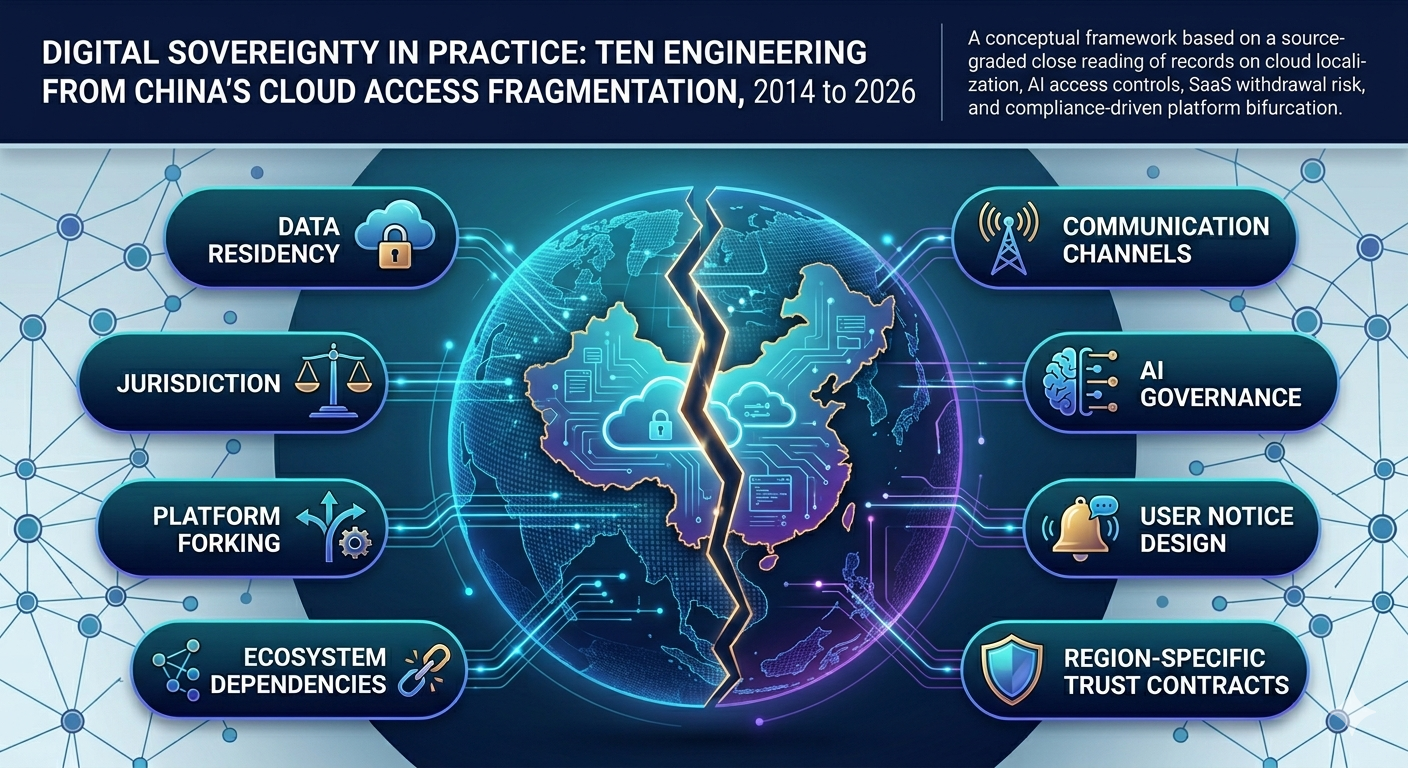
Published 10 April 2026 by Zenith Law
Cross-border SaaS delivery in China now follows a partitioned operating model shaped by regulatory sovereignty, data localization mandates, platform governance decisions, and geopolitical risk. This analysis reconstructs that model from fifteen li...
Published 9 April 2026 by Zenith Law
On 30 and 31 March 2026, malicious axios package versions on npm introduced a counterfeit dependency that executed install-time malware delivery across macOS, Windows, and Linux. This revision maps each material claim to explicit sources and separ...